Anti-money laundering checks are essential. If you are moving money, buying property, opening accounts, or dealing with regulated firms, identity checks are part of the deal. Fine. Nobody sensible wants the system wide open to fraudsters, launderers, or impersonators.
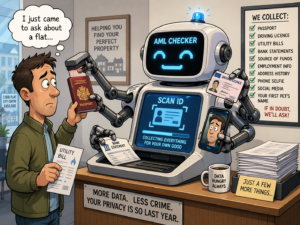
The trend in the property and financial sectors is alarmingly expanding the limits of what is reasonable under the guise of AML compliance.
We are seeing more firms, including estate agents and financial businesses, pushing people into paid third-party AML systems as if it is routine. Sometimes the charge is put on the client; other times, on the buyer, who is not the firm’s client, did not choose it, and is not getting legal advice—just trying to buy a house, but is required to upload personal documents to another platform and pay for them.
That is where this starts to stink.
AML Is One Thing. Data Hunger Is Another.
There is a critical distinction between necessary identity verification and the growing industry profiting from excessive personal data collection.
A firm can have legal obligations under anti-money laundering rules. That does not automatically mean every extra layer of outsourced checking, every extra fee, and every extra demand for personal information is justified.
Too often, it looks like firms have stopped asking the basic question: what is actually necessary here?
Instead, the process becomes:
Upload your passport. Now a selfie. Now, proof of address. Now answer questions. Now let the app scan your face. Now let it match you against databases you have never heard of. Now pay for it.
And if you object, the answer is usually some variation of: “It’s for compliance.”
That line is doing a lot of heavy lifting.
“You’re Not Even My Firm”
One of the maddest parts of this is the way the burden is shoved onto people who are not even the business’s customers, and they are demanded to do it.
Take estate agents. A buyer may have had no say whatsoever in which estate agent is involved in the transaction. The seller instructs the agent. The buyer is simply the other side of the deal. Yet the buyer can still find themselves being funnelled into a paid third-party ID system, handing over deeply personal information to a company they have never heard of, because somebody somewhere has decided this is now standard practice.
That should bother people more than it does.
Because once you accept that model, it spreads. More platforms. More data capture. More accounts. More copies of the same sensitive documents are floating around the internet. More businesses are normalising the idea that private identity material can be demanded as a routine gateway toll.
The Honey Pot Problem
Every one of these outsourced AML platforms becomes another lovely target for criminals.
Passports. Driving licences. Utility bills. Dates of birth. Home addresses. Banking links. Selfie verification data. Sometimes, biometric matching. Sometimes, a politically exposed person is screened. Sometimes, source-of-funds information. All of it stacked up in one place, or linked across multiple places.
Brilliant. Just what the world needed. Another honey pot.
And when firms say, “Don’t worry, we use a trusted third party,” that is not especially comforting. Plenty of trusted third parties turn out not to be so trustworthy after a breach, ransomware attack, takeover, insolvency, or data policy rewrite.
That is the point. The risk does not disappear because it has been outsourced. In many ways, it gets worse.
What Happens If the AML Checker Goes Bust?
This is where the whole thing gets very murky very fast.
What happens to all that data if the AML provider goes bust?
Who controls it then?
Who has access to the servers, backups, archives and logs?
What if the assets are sold?
What if another company buys the business?
What if the business is restructured and the data moves with it?
What if the data is stored abroad?
What if the provider changes subcontractors behind the scenes?
What if nobody at the front end — not the estate agent, not the adviser, not the poor soul at the desk telling you to upload your face — can actually explain any of this?
That is not paranoia. That is basic grown-up thinking.
If businesses are going to force people into third-party data systems, they should be able to explain clearly and confidently who holds the data, how long it is kept, what it is used for, what happens if the supplier fails, and how it is deleted when no longer needed.
In a frightening number of cases, they plainly cannot.
Compliance Theatre
Much of this process now resembles performative compliance—prioritising checklists and appearances over true risk management.
Someone buys a software package. It gives the firm a neat dashboard and a tick-box audit trail. The staff are told it is safer, easier and more robust. The public gets pushed through it because that is now “the process.” The cost gets passed on. The data exposure gets passed on. The inconvenience gets passed on.
And everyone pretends this is just what the regulations require.
Usually, it is not.
The regulations require firms to know who they are dealing with and assess risk properly. They do not require thoughtless overcollection. They do not require firms to gather every possible scrap of data because the software makes it easy to do so. They do not require businesses to normalise endless outsourcing without asking whether the cure is becoming nearly as bad as the disease.
Data Protection Should Mean Something
There is a principle in data protection law called minimisation.
That means you take only what you need.
Not what the app asks for. What you actually need—not every feature the app or salesperson suggests.
That principle matters because once identity data is spread across multiple systems and providers, the individual quickly loses control over it. Their documents are no longer displayed across a desk to a single regulated professional. They are digitised, uploaded, copied, stored, matched, retained, processed and possibly reprocessed by a web of third parties the individual has never met.
That is not a small step. That is a fundamental shift.
And the public is being conditioned to shrug and accept it.
Who Bears the Risk?
This is the part that annoys me most.
Firms get the audit trail. Software companies get the fees. The process speeds up. Liability becomes a fog of outsourced contracts and unread privacy notices.
The software companies get the fees.
The process gets faster for the business.
The liability is diffused into a fog of outsourced contracts and privacy notices nobody reads.
The software companies get the fees.
The process gets faster for the business.
The liability is diffused into a fog of outsourced contracts and privacy notices nobody reads.
But if the data leaks, who bears the real-world risk?
The individual.
The buyer whose passport copy is now doing laps around the dark web. An ordinary person’s private identification may be exposed.
The person who did not even choose the firm demanding the check in the first place.
The person who did not even choose the firm demanding the check in the first place.
This is the central flaw: convenience is handed to firms and tech vendors, but real-world data risks are unfairly pushed onto individuals.
A Sensible Approach Still Exists
None of this means firms should stop doing AML. That would be idiotic.
It means firms should stop pretending that more outsourcing, more fees and more data capture automatically equals better compliance.
Imagine a better approach—and push for it.
Carry out proper checks. Use third-party tools only where they genuinely add something. Collect the minimum necessary.
Be honest about what the provider does.
Explain where the data goes.
Explain how long it stays there.
Explain what happens if the provider is sold, fails or changes hands.
Offer a non-digital route where appropriate.
Instead, demand clear explanations and insist on the protection of your data. Challenge unnecessary data requests and ask firms to justify them.
Be honest about what the provider does.
Explain where the data goes.
Explain how long it stays there.
Explain what happens if the provider is sold, fails or changes hands.
Offer a non-digital route where appropriate.
Instead, demand clear explanations and insist on the protection of your data. Challenge unnecessary data requests and ask firms to justify them.
That is not “modernisation.” A lot of the time, it is just laziness dressed up as compliance.
Final Thought
AML rules exist for a reason. But there is a line between sensible verification and an industrial-scale appetite for data.
Some firms crossed that line a while ago.
The public is now being asked to hand over ever more personal information, to ever more third parties, for ever more routine transactions, often while paying for it themselves and with very little clarity about where that data ends up. That is not a minor admin issue.
It is a data protection problem. It is a cybersecurity problem. And increasingly, it is a common-sense problem.
When compliance justifies routine and excessive data collection, the promise of protection is lost, replaced by an unchecked appetite for data.
At J.J. Taylor & Co we will only ever ask for the bare minimum information necessary and also delete information as soon as we are able in the regulatory environment. If you want to talk more about this please don’t hesitate to contract us!